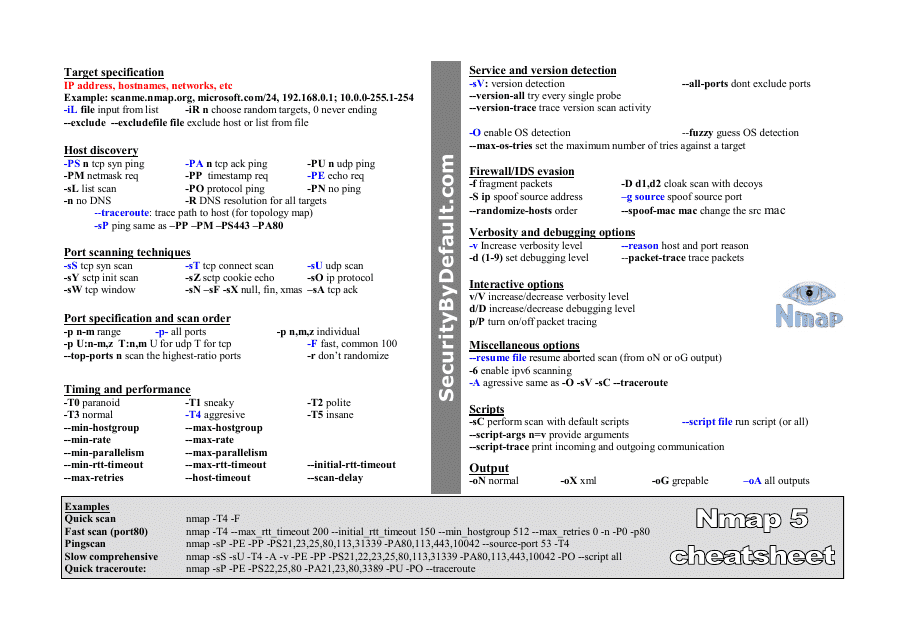
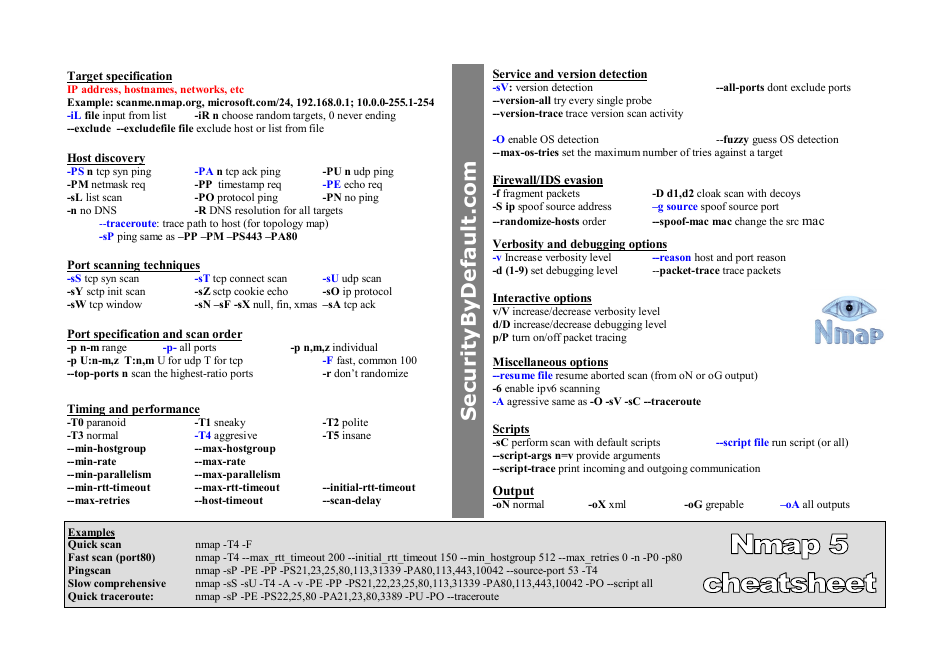
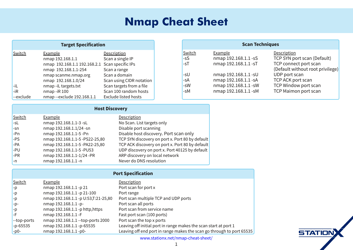
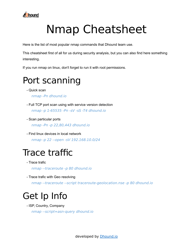
Nmap 5 Cheat Sheet
Nmap 5 Cheat Sheet is a document that provides a quick reference guide for using the Nmap network scanning tool. It helps users understand the various options and commands available in Nmap version 5.
FAQ
Q: What is Nmap?
A: Nmap is a network scanning tool used to discover hosts and services on a computer network.
Q: What can Nmap be used for?
A: Nmap can be used for network inventory, managing service upgrade schedules, monitoring host or service uptime, and probing firewall rule-sets.
Q: How do I use Nmap?
A: Nmap is a command-line tool that can be used to perform various network scanning tasks. You can specify target hosts or IP addresses and choose from a wide range of scan types and options.
Q: What are some common Nmap scan types?
A: Some common Nmap scan types include TCP connect scan, SYN scan, UDP scan, and OS detection scan.
Q: Can Nmap be used for security testing?
A: Yes, Nmap is often used for security testing and vulnerability assessment. It can identify open ports, detect vulnerable services, and perform network mapping.
Q: Is Nmap legal to use?
A: Yes, Nmap is legal to use as long as it is used responsibly and ethically. It should only be used on networks and systems that you have permission to scan.